In this article, we’ll look at the issue of website cybersecurity for web developers. From the main scams you need to know about to solutions such as VPNs and other security measures (see our Betternet Review as one provider we recommend), we’ve got the information you need to build and maintain secure websites that protect your customer data and prevent a malicious attack.
Why websites need to be secure
There are various drivers behind maintaining a secure website, and these go far beyond preventing financial damage. For example:
- To maintain your brand credentials and reputation in the market
- To prevent customer data from being illegally accessed (which can lead to fines and legal action in some cases)
- To ensure that customers trust your website and are happy to use it.
- To ensure that your website doesn’t become a security danger to other businesses, public sites, and customers by spreading malware.
- To avoid falling foul of GDPR and other relevant legislation
- To avoid the financial fallout which comes from a security breach – which can be the end of a small business in particular.
The different types of a website cybersecurity attack
There are four main types of attack that web developers need to know about:
- Phishing scams – where hackers send communications to customers that are designed to look authentic, persuading them to hand over sensitive data unwittingly.
- Insider threats – notoriously hard to uncover and can be either unwitting or intentional. An example of the former would be an employee opening up a phishing email by accident and allowing a virus to enter the company network. A malicious example could be an employee stealing customer data for commercial gains.
- DoS – Denial of Service attacks – where a website is flooded with ‘fake’ traffic, causing it to go down and to prevent legitimate users from accessing the service. Again, this type of attack is notoriously difficult to detect.
- Malware – the most common type of attack, where an individual will inadvertently download a malicious program which destroys or disrupts the website or operating system. Some of these have been extremely high profile in recent years and can act as viruses on a global scale.
Why carry out regular website security health checks?
All businesses have controls and processes in place to safeguard their operation and websites must be encompassed within this business continuity planning. Most commercial websites today are far more than simply brochure sites and instead offer fully-fledged e-commerce facilities, meaning that customer data must be managed and safeguarded in line with strict legislation.
By regularly reviewing the IT processes in place – ideally, as part of a recognized framework such as the ISO management standards – a robust system of detection and defence can be maintained. Incorporating Managed Detection and Response (MDR) services can further enhance this system by providing continuous monitoring and automated threat detection, allowing for swift identification and resolution of potential security issues.
Remember, regular audits are needed to check for any weak points in the systems and areas where possible breaches might occur.
This is essential on a regular basis because new types of cybersecurity attack are being developed and released all of the time by motivated and sophisticated hackers who see the financial gain in gathering customer data, or who simply enjoy the challenge of bringing commercial websites down for their own entertainment (or for hefty ransoms, in the case of ransomware attacks.
By keeping up with your cyber hygiene, you don’t just safeguard your own website and business – you also prevent identity theft from seriously affecting the lives of your customers. Neglecting cybersecurity, on the other hand, might well harm your reputation enough to put you plain out of business.
The most important site security health checks
Every business will have its own process for reviewing the people, processes, hardware, and software that are impacted by the website’s cybersecurity strategy. Specific areas for web devs to regularly audit and assess for integrity and best-in-class levels of protection include:
Malware and vulnerability scans
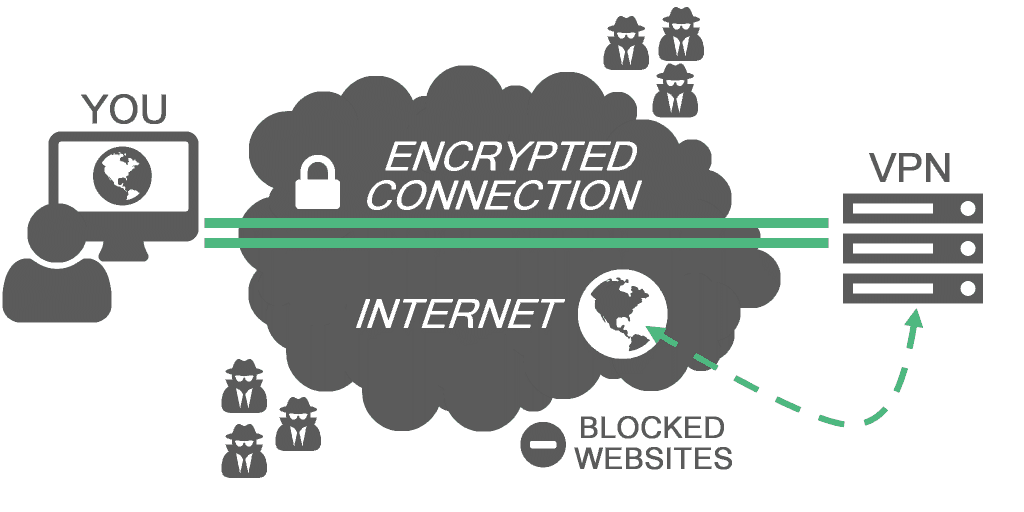
Malware looks for security weaknesses in your website code and exploits it by launching an attack. Sophisticated tools exist to carry out automatic scanning and identification of any vulnerable areas, flagging up potential fixes which can then be deployed. VPNs can also help by providing a secure means of accessing WiFi when working remotely, by cloaking your IP address and preventing any hackers from accessing your website. If your site was infected by WordPress malware, then we recommend that you check this WordPress malware removal guide on how to clean up your website.
DDoS and bot protection
Again, off the shelf products exist to protect against Denial of Service and botware attacks, and specialist providers exist to provide regular reviews of threats and ongoing protection against attacks.
Malware removal
Use security programs here that identify any malware and which remove it. VPNs and antivirus software should be combined for the most robust degree of protection. The antivirus software will be updated at the source with the latest attacks and be ready to identify and prevent them from accessing your website. In turn, the VPN will protect by shielding the IP address and by encrypting data to avoid any theft.
Unauthorized access detection
Again, software packages exist to flag up any malicious and unauthorized access of your website’s back end, allowing you to reset security and to reinforce the safety protocols and security layers of your site. A VPN will protect you from any spies by shielding and encrypting your data.
How to avoid threats
Website security is of paramount importance in today’s digital age. Hackers and cybercriminals are always looking for ways to exploit vulnerabilities and gain unauthorized access to websites. However, there are certain measures that website owners can take to mitigate such threats. One such measure is to implement WP Force SSL to your WordPress site, which ensures that all communication between the website and its users is encrypted and secure. Another useful plugin is WP Login Lockdown, which limits the number of login attempts and helps prevent brute-force attacks. By using these plugins and staying vigilant about website security, website owners can protect themselves and their users from potential threats.
Use a VPN
A Virtual Private Network or VPN, such as Betternet can help to maintain the integrity and privacy of your website. Not only does a VPN provide a secure ‘tunnel’ for data to travel between, but it also encrypts data so that it can’t be scanned or accessed in any way. IP addresses are also cloaked and shielded for anonymity. For security, it is recommended to VPN test your provider afterwards.
Invest in IDaaS
IDaaS (Identity-as-a-Service) allows organizations to outsource identity and access management to a third-party provider. Investing in IDaaS can save costs, improve security, enable easy scaling, and provide a seamless login experience. With experts handling IAM, companies can focus resources on core business goals. IDaaS is a smart investment for streamlining IAM while enhancing productivity and customer satisfaction.
Business continuity
As well a regularly reviewing these threats, businesses with a website should also have clear processes in place to deal with any attack that does occur. Many businesses simply have no clear process and timescale in place for dealing with an identified problem and communicating it – and the planned solutions – to their stakeholder groups. Without rapid management and resolution, cybersecurity breaches can rapidly magnify and cause issues of unprecedented damage.
In short, if you are a web developer, it is time to get to grips with cybersecurity and the tools needed to maintain it across your websites. The good news is that there are plenty of affordable and extremely good off-the-shelf systems and software packages that are designed to protect digital assets against all emerging threats. Just make sure you sign up to them and use them fully – keeping all versions updated and deploying all software updates, in order to stay one step ahead of malicious cybercriminals!